Searchsploit Review , Damn Small Vulnerable Web alternatives
Di: Ava
The best software alternatives to replace osquery with extended reviews, project statistics, and tool comparisons. The best software alternatives to replace fsociety with extended reviews, project statistics, and tool comparisons.
The best software alternatives to replace vulnerability-alerter with extended reviews, project statistics, and tool comparisons.
Damn Small Vulnerable Web alternatives
The best software alternatives to replace Gitrob with extended reviews, project statistics, and tool comparisons. The best software alternatives to replace Wappalyzer with extended reviews, project statistics, and tool comparisons. The best software alternatives to replace DataSploit with extended reviews, project statistics, and tool comparisons.
The best software alternatives to replace Infoga with extended reviews, project statistics, and tool comparisons.
This is the official repository of The Exploit Database, a project sponsored by Offensive Security. The Exploit Database is an archive of public exploits and corresponding vulnerable software,
TryHackMe — Lookup Walkthrough Objective The goal of this room is to exploit various vulnerabilities, escalate privileges, and capture the flags by gaining unauthorized
The best software alternatives to replace Metagoofil with extended reviews, project statistics, and tool comparisons.
CVSS 9.8 CVE-2023-25136 — SSH-MITM
- theHarvester alternatives
- Damn Small Vulnerable Web alternatives
- TryHackMe — Lookup Walkthrough. Objective
- VulnWhisperer alternatives
The best software alternatives to replace Damn Small Vulnerable Web with extended reviews, project statistics, and tool comparisons. Review against searchsploit, or double check the URL/IP you’ve picked. Note: If you’re doing a bounty mission, leave your fox acid UI up after you’ve broken into a server.
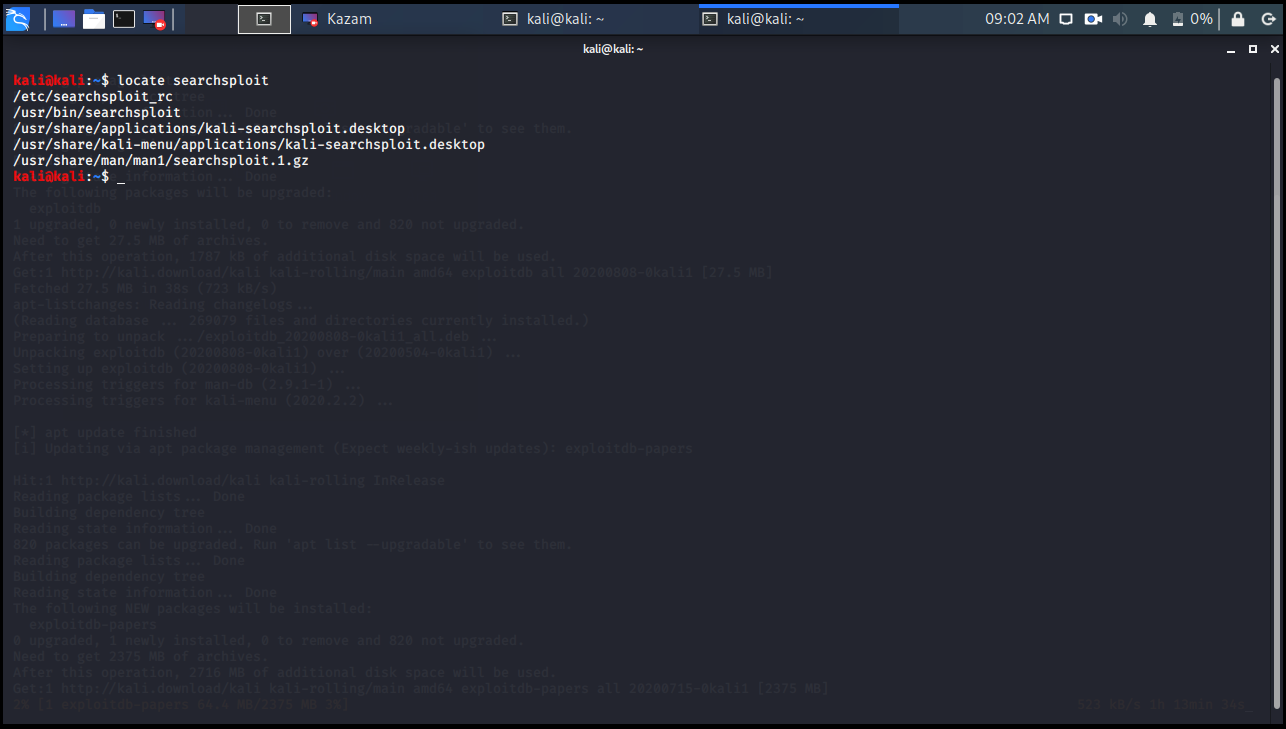
The best software alternatives to replace PEDA with extended reviews, project statistics, and tool comparisons. Now, to easily and quickly find the exploits we are interested in, there is a script written in python, where you call it Searchsploit. The best software alternatives to replace DirSearch (Go) with extended reviews, project statistics, and tool comparisons.
The best software alternatives to replace RTA with extended reviews, project statistics, and tool comparisons. SearchSploit Included with this repository is the SearchSploit utility, which will allow you to search through exploits, shellcodes and papers (if installed) using one or more terms. For more
The best software alternatives to replace PTF with extended reviews, project statistics, and tool comparisons. Installing Searchsploit on Linux Although Kali is already available on Linux, you can download it from GitHub to install it on other Linux systems. Finish the setup with the

The best software alternatives to replace AutoSploit with extended reviews, project statistics, and tool comparisons.
theHarvester alternatives
Searchsploit will search the local Exploit-DB repository on your Linux box. Provided you’ve updated the Searchsploit database, what you see here are the same results you’ll find on the The best software alternatives to replace LFI Suite with extended reviews, project statistics, and tool comparisons. This is the official repository of The Exploit Database, a project sponsored by Offensive Security. The Exploit Database is an archive of public exploits and corresponding vulnerable software,
During exam you can look through internet for information (eg Hacktrics) or exploits (exploidDB/Github). You just can’t use any AI engines and tools that can do automatic
Introduction to SearchSploit Included in the Exploit Database repository on GitHub is “searchsploit”, a command line search tool for Exploit This is the official repository of The Exploit Database, a project sponsored by Offensive Security. The Exploit Database is an archive of public exploits and corresponding vulnerable software,
The best software alternatives to replace Pompem with extended reviews, project statistics, and tool comparisons. The best software alternatives to replace Vulnreport with extended reviews, project statistics, and tool comparisons.
The best software alternatives to replace Belati with extended reviews, project statistics, and tool comparisons. Stage Two: Exploit At this point, I remembered the version numbers from my earlier searchsploit review and explored this path instead. Features Per-run intel folders → results are neatly organized by timestamp. Nmap integration → run scans directly from the tool (-sV -sC -p- by default). Keyword research: Runs searchsploit
The best software alternatives to replace web-hunter with extended reviews, project statistics, and tool comparisons.
vulnerability-alerter alternatives
Description OpenSSH version 9.2p1 was recently released with a fix for a double-free vulnerability. The vulnerability has a severe potential impact on OpenSSH servers and can
- Scs Folienschlauch 80°C | FLEXADUX® P 1 N hellgrau
- Seafood Restaurant Palm City Fl
- Screen: Create Sub-Task On Transition.
- Sebnitz: Nachträgliches Weihnachtsgeschenk Für Sportvereine
- Se Dansk Tv I Spanien _ Fodbold i TV i dag → Se Dagens Fodboldkampe i TV & Stream
- Seasonal Jobs At Disney , Disney Springs Jobs, Employment
- Seated Barbell Wrist Curl Hareketi Doğru Nasıl Yapılır
- Sea Turtle Rocks _ Sea Turtle Snorkeling Julian Rocks
- Secador De Pelo: Ventajas Y Desventajas De Su Uso
- Second-Funktion _ Diskrete zweite Ableitung